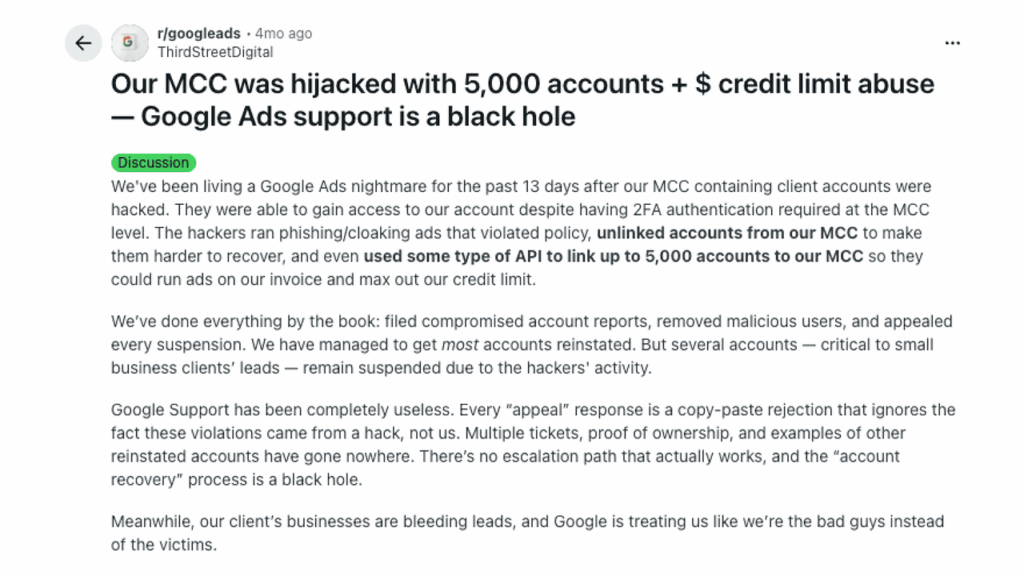
Google Ads agencies are reporting a sharp rise in MCC takeover attacks, where scammers use near-perfect phishing emails to steal full access to Google Ads Manager accounts. Even teams using two-factor authentication are getting hit.
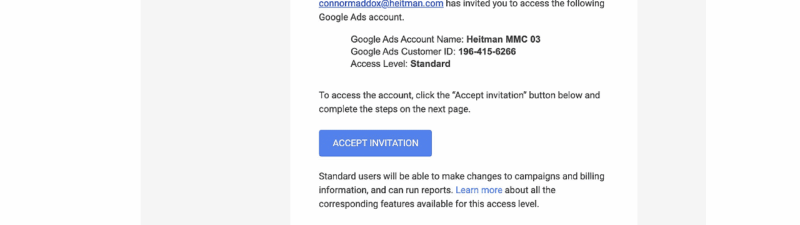
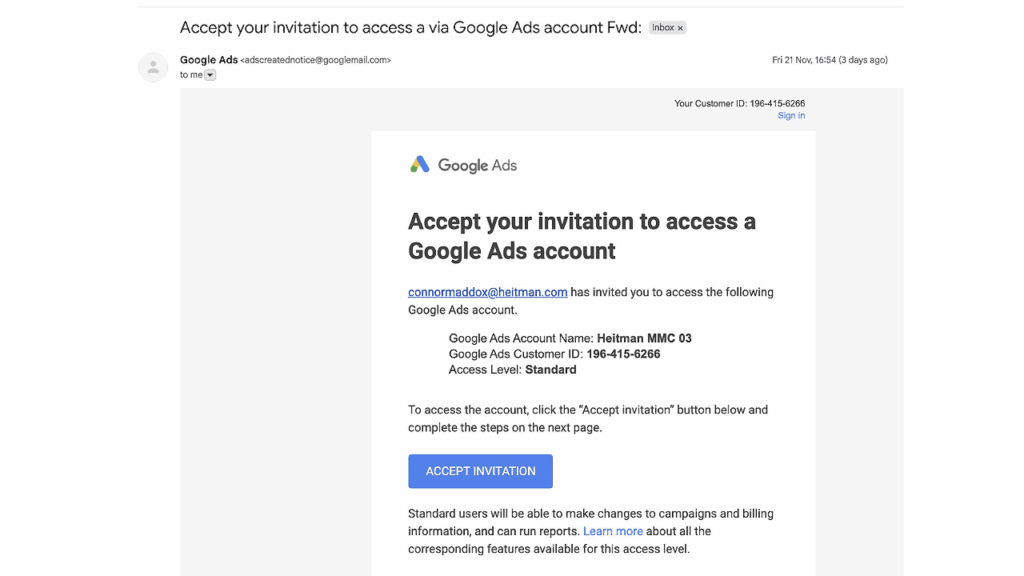
The scam mimics a legitimate Google access-invite email. Once the victim clicks, they’re taken to a fake login page hosted on Google Sites. Entering credentials hands attackers complete MCC access.
What happens next is brutal:
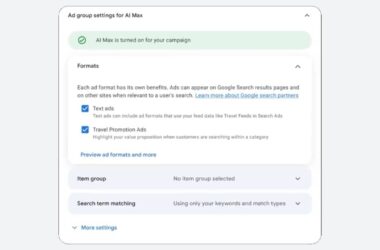
- Hackers add fake admins
- Link their own MCC
- Launch high-budget fraudulent campaigns
- Drain tens of thousands in spend within hours
Teams say the phishing emails are nearly indistinguishable from real Google messages, making them easy to fall for.
The fallout includes drained budgets, malware-linked ads, invalid activity flags, and operational chaos as agencies lose access to every client account.
Experts recommend verifying all URLs, checking invites inside your MCC, removing dormant users, and training teams to spot phishing, especially during holiday season spikes.
Until Google adds stronger MCC-level safeguards, vigilance is the only defense.
Read the full update here: Google Ads MCC takeover attacks are rising – here’s how the phishing scams work
This update was shared by Anu Adegbola.